事件描述:检测该异常事件意味着您服务器上开启了"Chargen/DNS/NTP/SNMP/SSDP"这些UDP端口服务,黑客通过向该ECS发送伪造源IP和源端口的恶意UDP查询包,迫使该ECS向受害者发起了UDP DDOS攻击
源IP: xx.xx.xx.xx 源PORT: 111 目的PORT: 963
攻击类型: SunRPC反射攻击
扫描IP频数: 3
扫描TCP包频数: 11480
持续时间(分钟): 55
事件说明: 检测该异常事件意味着您服务器上开启了"Chargen/DNS/NTP/SNMP/SSDP"这些UDP端口服务,黑客通过向该ECS发送伪造源IP和源端口的恶意UDP查询包,迫使该ECS向受害者发起了UDP DDOS攻击。
解决方案: 自查ECS中19、53、123、161、1900 UDP端口是否处于监听状态,若开启就关闭
自查步骤:
netstat -anp|grep :19
netstat -anp|grep :53
netstat -anp|grep :123
netstat -anp|grep :161
netstat -anp|grep :1900
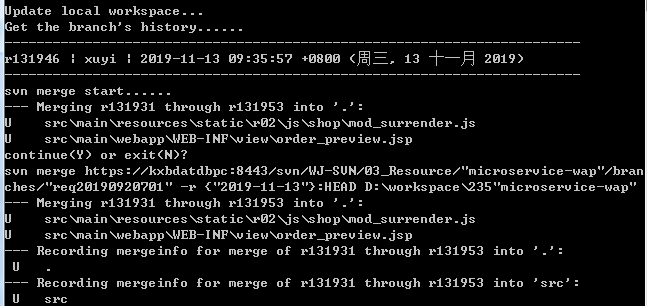
[root@AY1310231051059094d8Z server]# netstat -anp|grep :111
tcp 0 0 0.0.0.0:111 0.0.0.0:* LISTEN 1953/portmap
tcp 0 0 112.124.53.48:111 60.191.29.20:44964 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 139.196.13.106:30808 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:54912 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:38893 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 120.26.55.211:36599 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:39363 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:46023 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:57406 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:41479 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:39008 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 122.224.153.109:51125 ESTABLISHED 1953/portmap
tcp 0 0 112.124.53.48:111 123.59.52.206:44366 ESTABLISHED 1953/portmap
udp 0 0 0.0.0.0:111 0.0.0.0:* 1953/portmap
[root@AY1310231051059094d8Z server]# kill -9 1953
[root@*****server]# netstat -anp|grep :111
[root@****server]#

- 上一篇: 常被忽略的密码策略
- 下一篇: zookeeper未授权漏洞















评论